Index
TABLE OF CONTENTS
INTRODUCTION 7
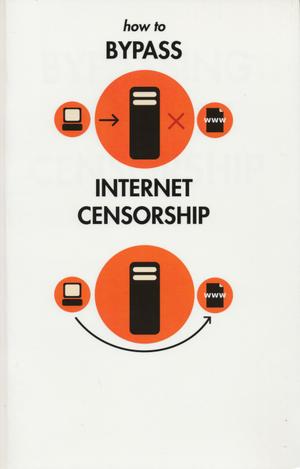
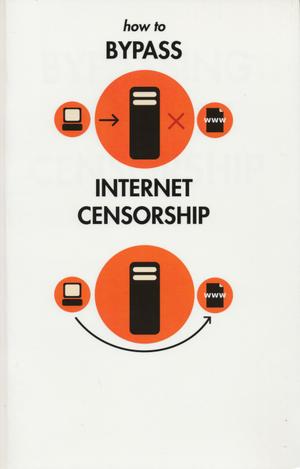
1. INTRODUCTION 9
2. ABOUT THIS MANUAL 13
BACKGROUND
3. BYPASSING INTERNET FILTERING 17
4. AM I BEING BLOCKED OR FILTERED? 19
5. DETECTION AND ANONIMITY 21
6. HOW THE INTERNET WORKS 25
7. WHO CONTROLS THE NET? 29
8. FILTERING TECHNIQUES 31
FIRST TECHNIQUES 35
9. SIMPLE TRICKS 37
10. WHAT IS ABOUT A WEB PROXY 43
11. USING PHPROXY 45
12. USING PSIPHON 49
13. WEB PROXY RISKS 55
ADVANCED TECHNIQUES 59
14. ADVANCED BACKGROUND 61
15. WHAT IS A HTTP PROXY? 69
16. INSTALLING SWITCHPROXY 79
17. USING SWITCHPROXY 83
18. TOR: THE ONION ROUTER 91
19. USING TOR BROWSER BUNDLE 103
20. USING TOR IM BROWSER BUNDLE 103
21. USING TOR WITH BRIDGES 109
22. ABOUT JONDO 113
TUNNELING 119
23. WHAT ARE VPN AND TUNNELING? 121
24. USING OPENVPN 125
25. SSH TUNNELLING 127
26. USING SOCKS PROXIES 131
HELPING OTHERS 141
27. INSTALLING A WEB PROXY 143
28. INSTALLING PHPROXY 145
29. INSTALLING PSIPHON 147
30. SETTING UP A TOR BRIDGE 151
31. RISKS OF OPERATING A PROXY 157
APPENDICES
32. RESOURCES 161